Release notes 2.9.2
|
Product |
EclecticIQ Platform |
|
Release version |
2.9.2 |
|
Release date |
19 April 2021 |
|
Summary |
Patch release |
|
Upgrade impact |
Medium |
|
Time to upgrade |
~15 minutes to upgrade
|
|
Time to migrate |
|
EclecticIQ Platform 2.9.2 is a patch release. It contains bug fixes.
For more information about new features, improvements, enhancements, deprecated features and components, and bug fixes we made available with release 2.9.1 and 2.9.0. See:
For more information about upgrading Elasticsearch to version 7.9.1, see Upgrade below.
For more information about enhancements and improvements, see What's changed below.
For more information about bugs we fixed, see Important bug fixes below.
For more information about security issues we addressed, see Security issues and mitigation actions below.
Download
Follow the links below to download installable packages for EclecticIQ Platform 2.9.2 and its dependencies.
For more information about setting up repositories, refer to the installation documentation for your target operating system.
|
EclecticIQ Platform and dependencies |
|
|
EclecticIQ Platform extensions |
In this release, the repository storing the platform dependency packages has been renamed from platform-dependencies-centos to platform-dependencies-centos-2.9.
Check the platform_deps_path variable and update its value accordingly, if necessary.
For more information, see Set up the repositories for CentOS and Set up the repositories for RHEL.
Upgrade
If you upgrade to EclecticIQ Platform 2.9.2 from 2.8.x or earlier, you must first run a pre-upgrade script in your current, not upgraded platform instance to prepare it to upgrade Elasticsearch to version 7.9.1, and to work correctly with Elasticsearch 7.x indices.
After successfully completing this preliminary procedure, you can start upgrading the platform to release 2.9.2.
If you skip this preliminary step, Elasticsearch 7.9.1 will not work as expected.
For more information about the Elasticsearch upgrade to version 7.9.1, see Prepare upgrading to Elasticsearch 7 for CentOS and Prepare upgrading to Elasticsearch 7 for RHEL.
For more information about automatically pruning log and metrics indices to limit their size and shard number, see Change data retention period of logs and metrics indices for CentOS and Change data retention period of logs and metrics indices for RHEL.
For more information about Elasticsearch 6.x deprecation, see Deprecations below.
Upgrade paths from release 2.0.x(.x) to 2.9.2:
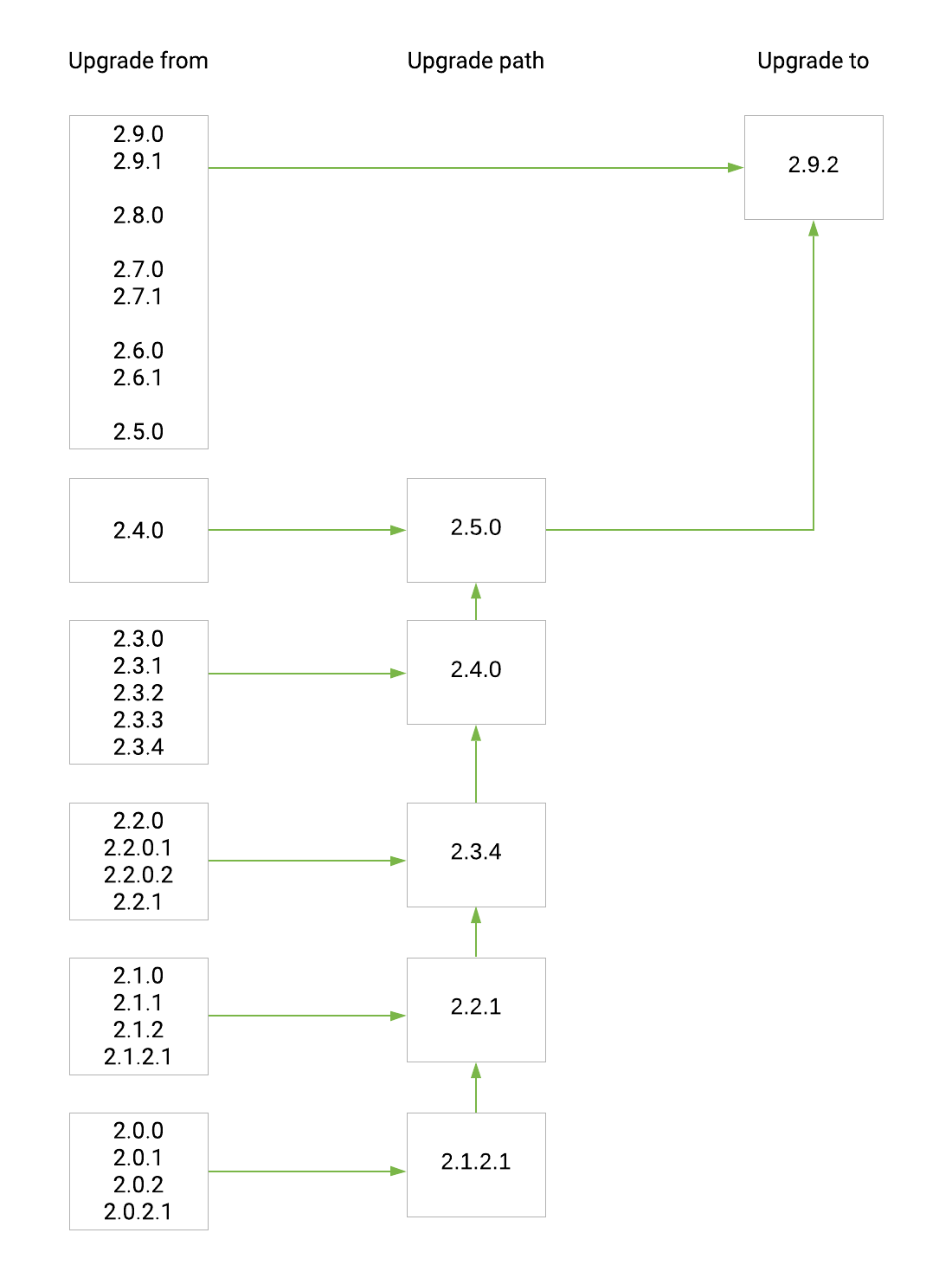
From release 2.5.0, the upgrades paths are tested using the EclecticIQ Platform install script compiled by Rundoc.
The script does not yet support upgrading the platform in a distributed environment.
As of now, it can only upgrade a platform instance that:
Runs on a single machine.
Was installed using the platform install script.
What's changed
Enforced content security policy
The platform now serves all pages with an explicit "Content-Security-Policy" header, mitigating possible XSS (cross-site scripting) and CSRF (cross-site request forgery) attacks.Improved UI responsiveness
Adding tags to entities is now faster on the platform UI.
Deprecations
Elasticsearch 6.8 end of life is November 20th 2020.
To have access to Elasticsearch product updates and security patches after this date, EclecticIQ Platform 2.9.0, 2.9.1, and 2.9.2 include an upgrade to Elasticsearch 7.9.1.
As a result, Elasticsearch versions earlier than 6.8.0 and Elasticsearch index versions earlier than 6.0.0 are no longer supported.
For more information about the Elasticsearch upgrade to version 7.9.1, see Prepare upgrading to Elasticsearch 7 for CentOS and Prepare upgrading to Elasticsearch 7 for RHEL.
Deprecated operating systems
As of release 2.9.0, support for the following operating systems is deprecated:
CentOS 7.8 (2003)
CentOS 7.7 (1908)
CentOS 7.6 (1810)
Red Hat Enterprise Linux 7.8
Red Hat Enterprise Linux 7.7
Red Hat Enterprise Linux 7.6
Ubuntu Server 16.04 Xenial Xerus
CentOS 7.6 (1810), 7.7 (1908), and 7.8 (2003), and Red Hat Enterprise Linux 7.6, 7.7, and 7.8 are compatible with release 2.9.x.
However, they are not supported.
Ubuntu Server is no longer supported.
The following operating systems are supported:
CentOS 7 latest release – currently CentOS 7.9 (2009)
Red Hat Enterprise Linux 7 latest release – currently Red Hat Enterprise Linux 7.9
Important bug fixes
This section is not an exhaustive list of all the important bug fixes we shipped with this release.
XSS possible through the /files/{ID}/media endpoint
Files containing a malicious Javascript payload would be executed when opened in the browser using the /files/{ID}/media endpoint. This is addressed in EIQ-2021-0006.XSS possible through HTML files attached to entity
HTML files containing a mailicious payload in its style tags would be executed when the entity it is attached to is loaded in the platform. This is addressed in EIQ-2021-0005.Password resets could be abused to spam administrator email accounts
A user could abuse the password reset feature to send an unlimited number of emails to administrator accounts that manage the groups the user belongs to.
Now, a user can send a maximum of 3 password reset requests per day. This can be set in platform_settings.py with the parameter: MAX_RESET_PASSWORD_PER_DAY .Users are able to create entities in groups where they should only have read permissions
A user could create entities in the Allowed sources that they are assigned to, where they should have only read permissions unless explicitly assigned to that group. This is addressed in EIQ-2021-0007.Incoming feeds fail subsequent runs after one partial failure
Incoming feeds would fail in subsequent runs if it previously encountered a partial failure, such as encountering an error after downloading at least one package.
Now, incoming feeds should correctly handle these partial failures and allow subsequent feeds to run.Discovery rules may stall in "Running" state
Discovery rules may get stuck in a perpetual "Running" state when several platform tasks are attempting to run at the same time. The issue affects any platform tasks, not just discovery rules. Now, the platform is stricter on handling simultaneously running tasks, preventing this issue.
Known issues
When you configure the platform databases during a platform installation or upgrade procedure, you must specify passwords for the databases.
Systemd splits log lines exceeding 2048 characters into 2 or more lines.
As a result, log lines exceeding 2048 characters become invalid JSON, causing Logstash to be unable to parse them.When more than 1000 entities are loaded on the graph, it is not possible to load related entities and observables by right-clicking an entity on the graph, and then by selecting Load entities Load observables, or Load entities by observable
When creating groups in the graph, it is not possible to merge multiple groups to one.
If an ingestion process crashes while data is being ingested by the platform, data may not always sync to Elasticsearch.
Between consecutive outgoing feed tasks, the platform may increase resource usage.
This may produce very high memory consumption over time.
Security issues and mitigation actions
The following table lists known security issues, their severity, and the corresponding mitigation actions.
The state of an issue indicates whether a bug is still open, or if it was fixed in this release.
For more information, see All security issues and mitigation actions for a complete and up-to-date overview of open and fixed security issues.
|
ID |
CVE |
Description |
Severity |
Status |
Affected versions |
|
- |
Users could create entities in Source Groups indirectly assigned through Groups, instead of only being able to create entities in Groups they are directly assigned to. |
1 - LOW |
|
2.9.1 and earlier. |
|
|
- |
SVG file upload could allow cross-site scripting (XSS) |
2 - MEDIUM |
|
2.9.1 and earlier. |
|
|
- |
HTML injection through the GUI |
2 - MEDIUM |
|
2.9.1 and earlier. |
|
|
CairoSVG is vulnerable to regular expression denial of service |
2 - MEDIUM |
|
2.9.1 and earlier. |
||
|
PySAML2 improper verification of cryptographic signature |
2 - MEDIUM |
Planned for 2.10.0 |
2.9.1 and earlier. |
||
|
Pillow is vulnerable to buffer overflow |
2 - MEDIUM |
|
2.9.1 and earlier. |
Contact
For any questions, and to share your feedback about the documentation, contact us at [email protected] .